In my last post , I spoke about the security, cost, and workflow benefits of SSO. But if you perform an online search for SSO solutions, you’ll likely also come across Privileged Access Management, Identity Access Management, and password management technologies.
This can be very overwhelming so let’s clear up the differences between each technology.
First of all, Identity Access Management (IAM) is the parent category of all access security technology. So Privileged Access Management, SSO, and password managers are all sub-categories of IAM.
Let’s further accentuate the dividing lines between each subcategory with some quick definitions:
- Privileged Access Management (PAM) – An authentication module that controls access to sensitive resources through permission restrictions.
- Password Manager – A program that securely stores all user credentials in one centralized location.
- Single Sign-on (SSO) – A user authentication process allowing users to securely log into multiple applications from a single set of credentials.
Many business owners think PAM and SSO technologies are interchangeable but they both play very distinct roles in a cybersecurity program.
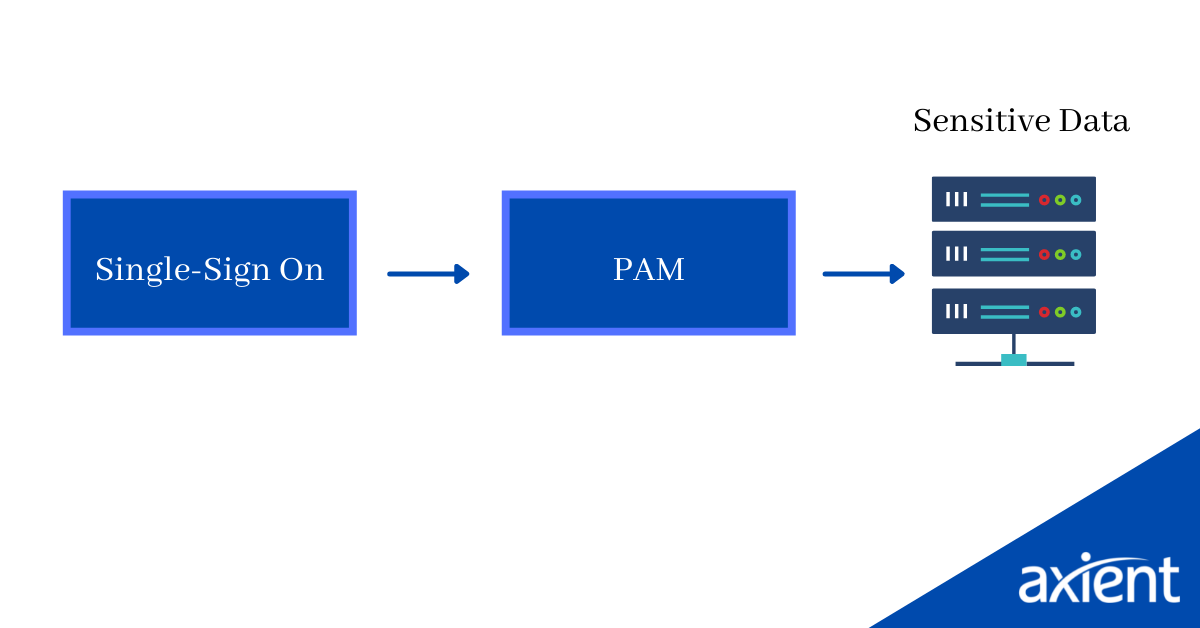
At a high level, the difference between the two lies in their defensive positions in the user access sequence.
SSO technology can be regarded as the gatekeeper to a private network. It ensures only authorized users are granted access to any of the apps used by an organization.
When a user’s initial access is approved by this first line of defense, the responsibility of securing deeper levels of access is passed onto a PAM solution. PAM solutions draw a hard line in the sand between users and sensitive resources, ensuring access to sensitive resources is only granted to those that absolutely require it.
So where do password managers fit into this equation?
Well, SSO solutions are not applicable in all scenarios. Some websites and applications are not compatible with the underlying mechanisms of SSOs, such as LDAP or SAML, and sometimes IT departments just forget to add new applications to the SSO system.
Password managers prevent workflow interruptions during these use-cases by automatically populating login credentials when SSO functionality isn’t possible.
SMBs should implement both an SSO and a password management solution. This will fill any access gaps created by websites that aren’t compatible with SSO while maintaining minimal login screen interruptions for those that are.
To minimise costs, these features should be available in a single product. At Axient, we support our clients with both SSO and password management capabilities neatly packaged into a single product offered by LastPass.
If you could only choose between a PAM solution and an SSO solution, which would it be and why? Drop me an email I’d love to know your thoughts.

 02 8338 3444
02 8338 3444